Last month, I moved out with my brother from my parents’ house. We’re still quite close to our current house (about a 2 minute drive away), but there are some things that I would like to be able to access remotely from my new place, and vice versa. This meant I had to create a VPN route to pass some traffic between two locations, such as for printing files and for backing up files off site.
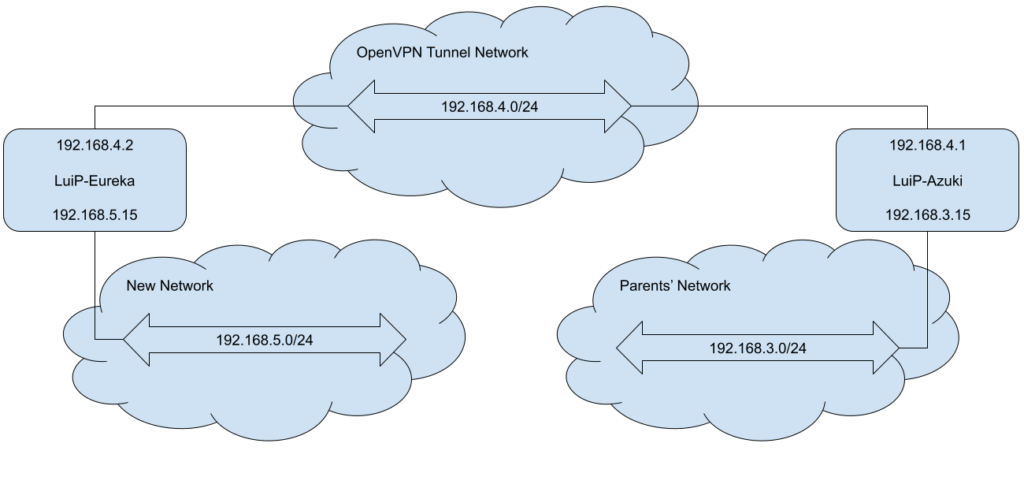
The solution I opted for was to use OpenVPN. I have an OpenVPN server at my parents’ place, so I set up another client at my new place to act as a VPN router. This way, other hosts from my 192.168.3.0 network don’t need to additional configuration to access hosts on the 192.168.5.0 network and vice versa.
In order to pass traffic back and forth between the two networks, I needed to configure the VPN client and the VPN server to forward traffic destined to different networks. To do this, on my VPN client on the .5 network, I configured it as follows:
- A static IP of 192.168.4.2 on the VPN interface,
- A static IP of 192.168.5.15 on the LAN interface, and
- A static route for 192.168.3.0/24 to forward to 192.168.4.1.
On the .3 network, I configured the VPN server as follows:
- A static IP of 192.168.4.1 on the VPN interface,
- A static IP of 192.168.3.15 on the LAN interface, and
- A static route for 192.168.5.0/24 to forward to 192.168.4.2.
To illustrate the IP addresses above, below is a high level network topology.
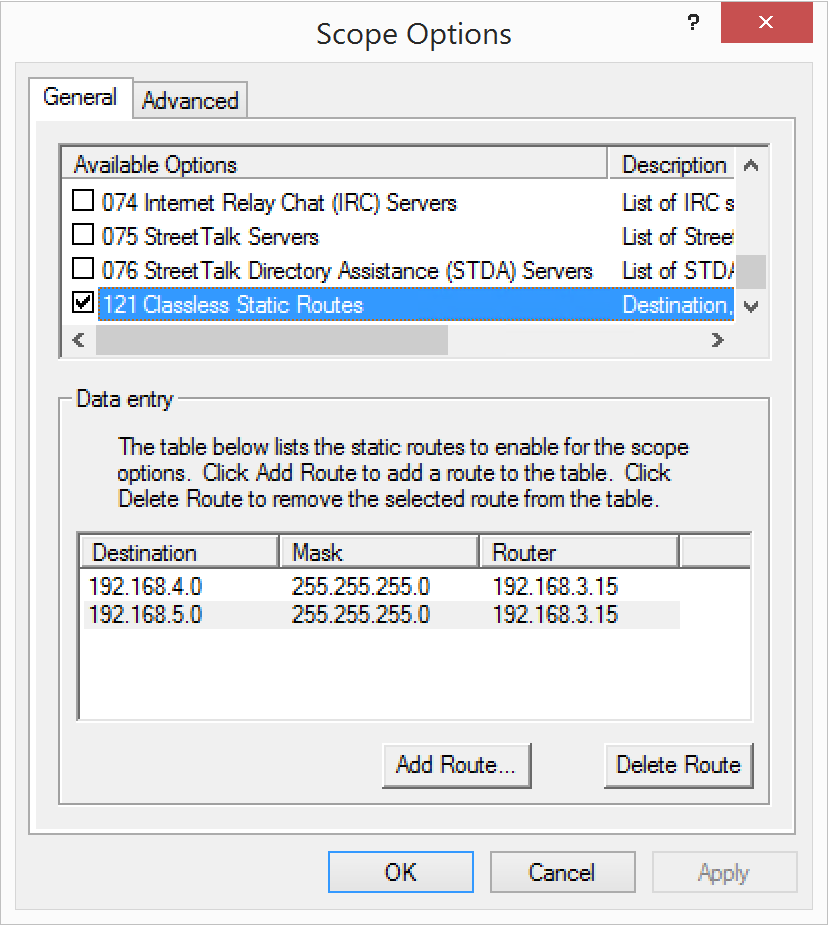
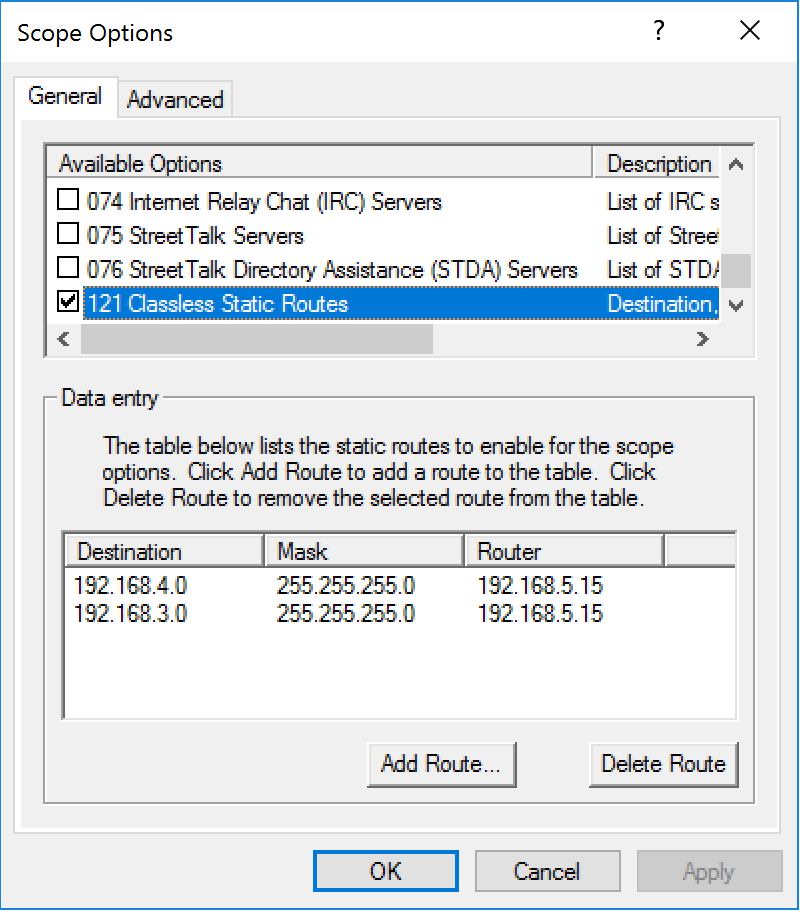
With the static routes in place, I need to inform all clients on the .5 network to send traffic destined to 192.168.3.0/24 to 192.168.5.15, and all clients on the .3 network to send traffic destined to 192.168.5.0/24 to 192.168.3.15. Since I’m using Windows DHCP Server on both sites, I added those routes to the Classless Static Route option. That way, all new clients connecting to the network will automatically get these routes:
On the OpenVPN side of things, I did have to adjust some flags in order to get things to properly work. For some reason that I was unable to root cause, when using UDP for transport, the VPN tunnel kept dropping packets when visiting my internal sites during the VPN session. I was seeing >30% packet loss that made the connection virtually unusable. After searching for similar issues from other people, I began to suspect an MTU issue, but setting the fragment flag to 1300, 1200, 1000 and even 500 alongside with the mssfix flag didn’t seem to remedy the problem.
To fix the problem, I had to swap to using TCP for the VPN tunnel in order to have a stable connection. Having no access to the intermediate nodes in the outside network, I can only suspect that packets were occasionally taking a different route between the sites that were causing them to be dropped somewhere. I do understand that TCP (for HTTPS) over TCP (for VPN tunnel) introduces a lot of overhead related to the nesting of sequence IDs and their associated sliding windows. Given that I wanted things to “just work” and the upload speed at my parents’ place is capped at 15 megabits per second, this seemed like a reasonable tradeoff than having my internal pages (like this blog when viewed inside my home network) continually time out. Interestingly, for pings, I still see a ~10% loss. That being said, when accessing hosts over the VPN, it seems to be hold up acceptably without a noticeable delay. Internal RDP seems to suffer more.
The end result is that I can now access devices on both networks from either network. I am able to print documents from my new place at my parents, place, and access files from my new place and vice versa. I eventually might swap my main server out of my parents’ place with the NAS I bought a few months back, but seeing how things are working as they should, I will hold off on it for now.
Anyways, that’s all I got this time around.
Until next time!
~Lui
[…] the beginning of the year, I talked about using OpenVPN to connect my parent’s network with my new place. The OpenVPN server was hosted on my Windows Server 2012 R2 machine, which I had recently […]